
HookWatch
Automated webhook monitoring for indie hackers & small teams
88 followers
Automated webhook monitoring for indie hackers & small teams
88 followers
Never miss a webhook again. HookWatch monitors, logs, and retries your webhooks automatically. Built for indie hackers and small teams. HookWatch monitors your webhook endpoints 24/7 and alerts you instantly when something breaks. Built for developers who need reliable monitoring without enterprise complexity. Simple setup, affordable pricing, peace of mind.








HookWatch
Hey Product Hunt! 👋
I'm thrilled to launch HookWatch today — a tool I've been building to solve a problem that's been driving me crazy for years.
The problem: Modern apps rely on webhooks, cron jobs, WebSocket connections, and now AI agents — but when they fail, they fail silently. No error page. No stack trace. Just... nothing happens. A Stripe payment webhook gets lost, a nightly backup script silently stops running, a WebSocket connection drops mid-session, an AI agent starts erroring out — and you don't find out until a customer complains or data is already gone.
I've been on the other side of that support ticket too many times. So I built HookWatch.
What is HookWatch?
It's four monitoring tools under one roof:
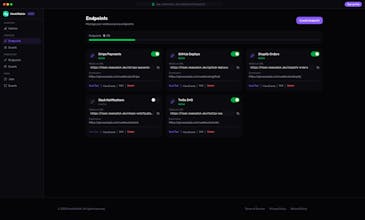
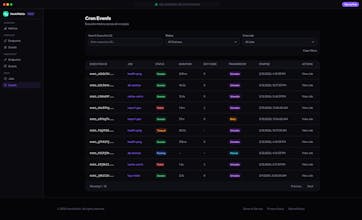
🔗 Webhook Monitor — Track every incoming webhook in real-time. Inspect full payloads, replay failed deliveries with one click, and get automatic retries with exponential backoff. We even have a unique request buffering feature: if your server goes down, HookWatch stores incoming webhooks and replays them when you're back online. Zero data loss.
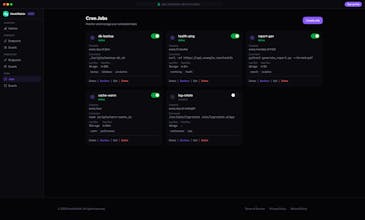
⏰ Cron Monitor — Schedule and monitor cron jobs with human-readable syntax. Write "every day at 2am" instead of decoding 0 2 * * *. Get full execution history with stdout/stderr, automatic retries, and instant alerts when something breaks. The CLI runs jobs locally with optional cloud sync — it works 100% offline.
🌐 WebSocket Monitor — A transparent proxy for your WebSocket connections that gives you complete visibility into bidirectional traffic. Point your client to a HookWatch proxy URL instead of the original server — we forward everything transparently while capturing every message in both directions. See live connections open and close, inspect full payloads (text and binary), filter by direction (inbound/outbound), and review complete message history. Debug dropped connections, validate payload formats, and investigate incidents — all without changing a single line of your application code.
🤖 MCP Proxy — Observability for AI agent tool calls. Monitor every MCP request/response, track latency (p50/p95/p99), and get alerts when your agents hit errors. If you're building with Claude or other LLMs, this gives you the visibility you've been missing.
What makes HookWatch different?
Four tools, one dashboard. Competitors focus on just one. We bundle webhooks + cron + WebSocket + MCP monitoring together.
Local-first CLI. Not just a web dashboard — our CLI is a first-class citizen. Forward webhooks to localhost, run cron jobs locally, get JSON output for scripting. Works offline.
Transparent proxying. Both for webhooks (request buffering when your server is down) and WebSockets (full bidirectional message capture). Zero code changes required.
Human-readable schedules. Stop Googling cron syntax. Write schedules in plain English.
AI-native from day one. MCP observability is built in, not bolted on.
I'd love to hear your feedback — what features would you want to see next? What integrations matter most to you?
Happy to answer any questions in the comments! 🚀
Webhooks are the backbone of automated billing and agent workflows. Curious how you're handling verification and tamper-proof logs once events fire — that layer’s becoming just as important as uptime.
HookWatch
@infrapulse Thanks for bringing this up — it's a critical layer we've built in from day one.
Inbound verification: Every endpoint can be configured with HMAC-SHA256 signature validation. We support common header formats out of the box — GitHub, Stripe, Slack, Shopify — or you can set a custom one. Invalid signatures get rejected with a 401 before anything is processed.
Outbound signing: When we deliver webhooks to your destination, we sign the payload so your app can verify it's genuinely from HookWatch.
Audit trail: Every event is stored immutably with full payload, headers, and timestamps. Every delivery attempt is logged with status codes, response times, and retry history.
Secrets can be rotated anytime from the dashboard — no downtime needed.
Silent webhook failures are such a pain to debug. Nothing worse than finding out days later that payment notifications just... stopped working and nobody noticed. How customizable is the retry logic? Like can you set exponential backoff per endpoint, or is it one-size-fits-all? Also wondering about log retention - do you purge after X days or is there a way to keep critical webhooks logged longer?
HookWatch
@mykola_kondratiuk Exactly this! Silent webhook failures are the worst — you only find out when a customer complains they never got their payment confirmation. That's literally why I built HookWatch 😅
Retry logic — fully customizable per endpoint. Exponential backoff, custom intervals, max retries — you configure each webhook independently. Stripe payment hooks and low-priority analytics pings shouldn't share the same retry strategy.
Log retention — depends on the plan, but you can flag critical webhooks for extended retention. Plus export is available if you need long-term archiving for compliance.
And the key piece: real-time alerts on first failure, so you're not waiting until retries are exhausted to find out something's broken.
Would love to hear what other pain points you've run into — always looking to make HookWatch better! 🙌