
Nix Capture
Capture API requests for bug reports in seconds
59 followers
Capture API requests for bug reports in seconds
59 followers
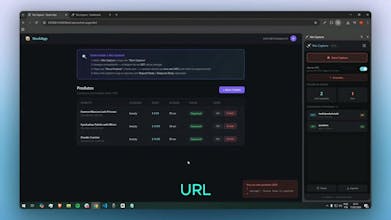
Bug reports often arrive without request context — no endpoint, no status code, just “it’s not working.” Nix Capture lets you record network requests while reproducing an issue and export everything engineers need in seconds. No DevTools. No technical knowledge required. Built for QA, support, and product teams who want actionable bug reports.







Nix Capture
This hits a real nerve. I've lost count of how many bug reports I've gotten that just say "it doesn't work" with a screenshot of a blank page. Having non-technical team members capture actual request context without opening DevTools is a smart approach.
Question: do you plan to support auto-redaction of auth tokens/sensitive headers before export? That would make it much easier for support teams to share captures without worrying about leaking credentials.
Nice launch, congrats!
Nix Capture
@a_kuzov Appreciate the question!
Yes — auto-redaction is something I’m actively considering.
The goal is to make sharing captures safer for support teams without adding friction to the debugging process, especially when sensitive headers like auth tokens are involved.
Nix Capture
@a_kuzov Hey! Just wanted to let you know we shipped an update based on your feedback.
Nix Capture now detects sensitive headers (like Authorization, cookies, and API keys) when exporting requests or copying a cURL, and lets the user choose whether to include them or remove them before sharing.
Really appreciate you raising that — it directly helped improve the product.
Nix Capture
@md_murtuza_ali Great question! and yes, sensitive data is something I’m actively thinking about.
Right now, the extension allows capturing headers like tokens when needed for debugging, since in many real-world cases they are essential to reproduce issues.
That said, this is also why the focus is on making the data visible and understandable, so teams can decide what to share safely when creating reports.
Improving masking and redaction options is something I’m considering as the product evolves.
Nix Capture
@md_murtuza_ali Hey! Just wanted to let you know we shipped an update based on your feedback.
Nix Capture now detects sensitive headers (like Authorization, cookies, and API keys) when exporting requests or copying a cURL, and lets the user choose whether to include them or remove them before sharing.
Really appreciate you raising that — it directly helped improve the product.
Nix Capture
Quick update: based on the feedback here, we just shipped a new safety layer in Nix Capture.
When exporting requests or copying a cURL, the extension now detects sensitive headers (like Authorization, cookies, and API keys) and lets you choose whether to:
include sensitive data
remove sensitive data before sharing
This was one of the most valuable discussions from this launch — really appreciate everyone who pointed it out 🙌
Nix Capture
Quick update — I’ve just added an English version of the demo video to make it easier for everyone to follow along.