
rmBug
Know exactly who's in your databases. People or machines.
5 followers
Know exactly who's in your databases. People or machines.
5 followers
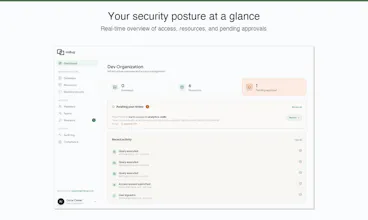
rmBug is built by the people who actually understand and have lived through the problem in the past. It starts with database access and related functionality for sure, but will expand into making sure all your data is as secure as it can be, all while keeping user (and developer) experience top priority. We have the features, but don't compete on features at all - we compete on making your life easier and more secure, without the associated expensive price-tag.




Hello hello. Mario here, one of the founders behind rmBug.
The domain has been sitting there for a while, waiting for a real problem and the right team. Secure data access turned out to be both. Luka and I kept running into it at every organization we worked in or worked with. Solutions exist, but they're either enterprise-only, require you to self-host, hide pricing behind a "contact us" wall, or they exist because of a recent wave they're hoping to ride.
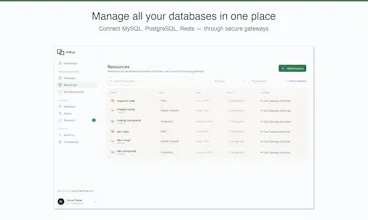
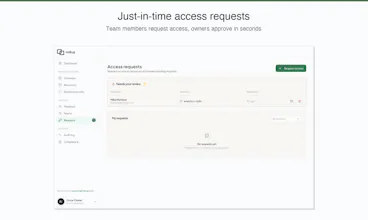
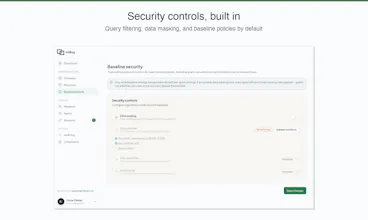
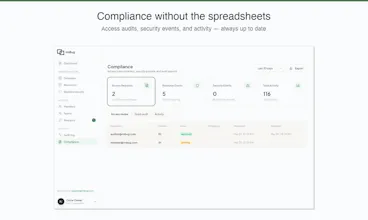
We want to make database access security as simple as 1-2-3. Today that starts with MySQL and PostgreSQL, with identity-based access for engineers, support teams, and AI agents out of the box. Every connection is tied to a real person or a named agent, with a full audit trail. From here, we want to expand into other areas that touch your data, with your input. Think end-customers with GDPR requests, third-party vendor access, compliance workflows. We want to build this because we know how it feels to not have it. All while keeping an affordable price-tag.
Happy to hear any feedback, jump on a call, or have you as a user. Let's make rmBug the standard for secure data access.
Hey, Luka here, the other half of rmBug.
The thing Mario's being polite about is that most database security today is basically theater. You set up SSO for your apps, IAM for your cloud, mTLS between your services, and then your database authenticates everyone as app_readonly. Twenty engineers, three microservices, and a contractor whose access was never revoked, all showing up as the same account.
I spent twenty years running infrastructure for companies dealing with HIPAA, SOC 2, and production databases that hundreds of people touched daily. The tools either cost six figures, took months to deploy, or made developers find workarounds instead of using them. I kept waiting for someone to build the obvious thing. Nobody did, so here we are.
We're building a proxy layer that fixes this without requiring you to rewire your stack. Connect through rmBug the same way you'd connect directly, using psql, DataGrip, dbt, whatever. Every session gets tied to a real person or a named agent. The migration is "change one connection string," not a quarter-long project.
Starting with MySQL and PostgreSQL. If you've ever had an incident review where someone asked "who ran that query?" and nobody could answer... come talk to us.