Launched this week

VulWall
Know your score. Fix what matters. Prove it.
13 followers
Know your score. Fix what matters. Prove it.
13 followers
VulWall gives companies without a security team a security score, step-by-step fixes in plain language, and a certificate to prove it. Free to start.







jared.so
Free tier as the real product, paid for the certificate is a sharp pricing flip. How do you keep the score honest as new CVE classes drop?
Thanks!
On the score: The honesty comes from rescanning, not curation. Every scan recalculates the score from scratch. There's no cumulative "you used to be a 92" carryover. So when a new CVE class lands in the next scan, it lands in your number.
Three concrete mechanisms keep it current:
1. Daily detection-signature updates. Our scanners pull updated CVE detection signatures from public security research repositories on a daily cron. When upstream maintainers ship a template for a freshly disclosed CVE, often within hours of disclosure, the next scheduled scan picks it up. We don't pin to a stale snapshot.
We focus on exploitable vulnerability classes: remote code execution, SQL injection, auth bypass, exposed admin panels, known-exploited CVEs, misconfigurations, subdomain takeovers. Pure informational findings (banner grabs with no exploit path) get filtered out so the score reflects real risk, not noise.
2. Recurring scans, not one-shot. Free is monthly, Pro is weekly. The dashboard score is always tied to the most recent scan. No manual "refresh" button, no stale snapshot you forgot was from March.
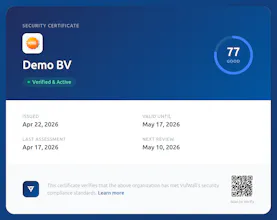
3. The certificate has a 30-day TTL. This is the part most people miss. The paid certificate isn't a perpetual badge. It expires 30 days after the last scan. Stop scanning, the cert expires. So a procurement team looking at a VulWall cert is seeing a result that's at most 30 days old, scored against signatures that are at most a day old.
Scoring itself is deterministic. Critical findings dominate the score by an order of magnitude over Medium ones, and age penalties stack on top. A Critical unfixed for 90+ days weighs about 2x a fresh one. Same formula for everyone, recalculated every scan.
Where it's honestly weakest: we inherit coverage from the upstream signature ecosystem, so a CVE class without a community detection rule won't move the score. And our scope is external web infrastructure, not your code dependencies, not your internal network. For dependency-level CVEs, pair us with something like Snyk.