Never build Permissions again. Zero-latency fine-grained authorization as a service for human, machine, and agentic identities.
This is the 4th launch from Permit.io. View more

Permit.io MCP Gateway
Launching today
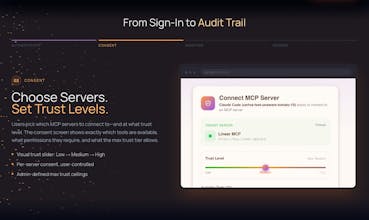
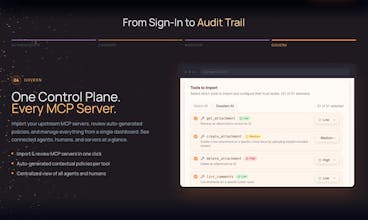
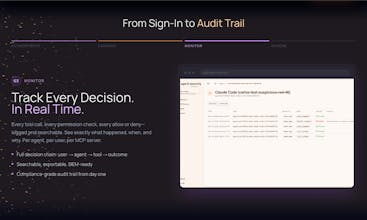
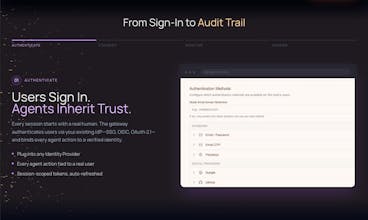
MCP lets AI agents connect to your tools, but its built-in auth is limited. There's no fine-grained authorization, no governance, and no connection to your existing IdP infrastructure. Permit MCP Gateway is a zero-trust proxy that adds what's missing to any MCP server without touching its code. Swap one URL and every tool call gets OAuth authentication, Zanzibar-style authorization, consent screens, and full decision logging. No SDK to install. No agents to rewrite. Works with any MCP server.



Free Options
Launch Team / Built With









Hey Product Hunt! David here, Solutions Engineer at Permit.io.
We just published two walkthroughs showing the MCP Gateway in action:
Enforce per-user trust levels on Linear's MCP (Developer vs PM access): https://docs.permit.io/permit-mcp-gateway/demos/linear-mcp-gateway
Gate an n8n automation workflow with real-time trust controls: https://docs.permit.io/permit-mcp-gateway/demos/n8n-linear-mcp-gateway
No changes to the underlying MCP servers — just drop the Gateway in front and control who (or what) can do what. Both demos take just a few minutes to set up. Would love to hear what MCPs you'd want to see demoed next!
Wow, this is really impressive 👋I love that you’re tackling such a tricky but crucial part of the stack , authorization and security are easy to overlook until something breaks. The fact that it works as a transparent proxy without touching agents or servers makes it feel much more approachable for real world use.
I’m curious too , how do teams usually start tackling the visibility and fine-grained control challenges? It seems like understanding what agents can do, and who’s authorizing them, is where most of the headaches come in.
How easy is it to roll this out across multiple MCP servers in a larger setup? Especially for teams managing different environments.
It would be helpful to see a simple dashboard or visual layer where teams can quickly understand who has access to what without digging into logs.
Most teams rushing into MCP are basically ignoring the “who can do what” problem until it blows up later, so the zero-trust proxy + one-URL integration is a very pragmatic approach. The delegated identity chain and audit logging are especially strong, that’s the kind of detail security teams actually care about in production.
Curious—how do you balance policy granularity vs. usability? At what point does fine-grained control become too complex for teams to realistically manage?
How does this handle performance under heavy load ?Zero latency sounds great curious what that looks like in real world benchmarks .
One thing I’d want to understand better is performance overhead. Since every request goes through the gateway, does it introduce noticeable latency in high frequency systems?