Never build Permissions again. Zero-latency fine-grained authorization as a service for human, machine, and agentic identities.
This is the 4th launch from Permit.io. View more

Permit MCP Gateway
Launched this week
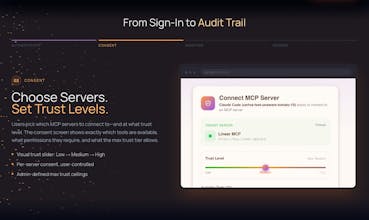
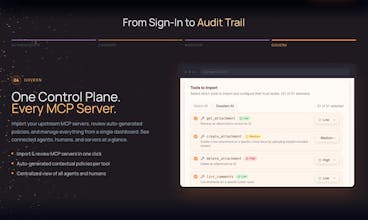
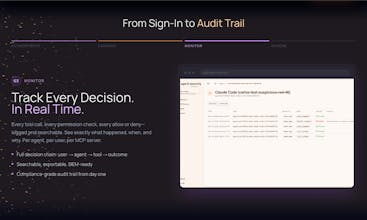
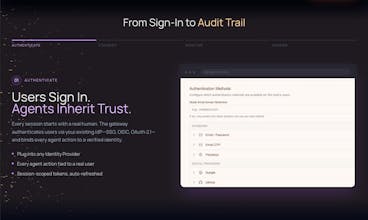
MCP lets AI agents connect to your tools, but its built-in auth is limited. There's no fine-grained authorization, no governance, and no connection to your existing IdP infrastructure. Permit MCP Gateway is a zero-trust proxy that adds what's missing to any MCP server without touching its code. Swap one URL and every tool call gets OAuth authentication, Zanzibar-style authorization, consent screens, and full decision logging. No SDK to install. No agents to rewrite. Works with any MCP server.



Free Options
Launch Team / Built With









Trufflow
Having audit trails is so important, so having the ability to know who authorized which agent is really nifty. Does Permit.io flag when policies fall outside standard best practices? Or does the auto-generation capability fully manage this such that no manual configuration is required after set up?
Permit.io
@lienchueh it's hybrid. We generate contextual policies that you can then modify/extend per your need. You're more than welcome to try it yourself in the product 😉
Hey Product Hunt! David here, Solutions Engineer at Permit.io.
We just published two walkthroughs showing the MCP Gateway in action:
Enforce per-user trust levels on Linear's MCP (Developer vs PM access): https://docs.permit.io/permit-mcp-gateway/demos/linear-mcp-gateway
Gate an n8n automation workflow with real-time trust controls: https://docs.permit.io/permit-mcp-gateway/demos/n8n-linear-mcp-gateway
No changes to the underlying MCP servers — just drop the Gateway in front and control who (or what) can do what. Both demos take just a few minutes to set up. Would love to hear what MCPs you'd want to see demoed next!
Formaly
This is Great!
Def gonna try this out!